Use Case 1: Unexpected Money Request
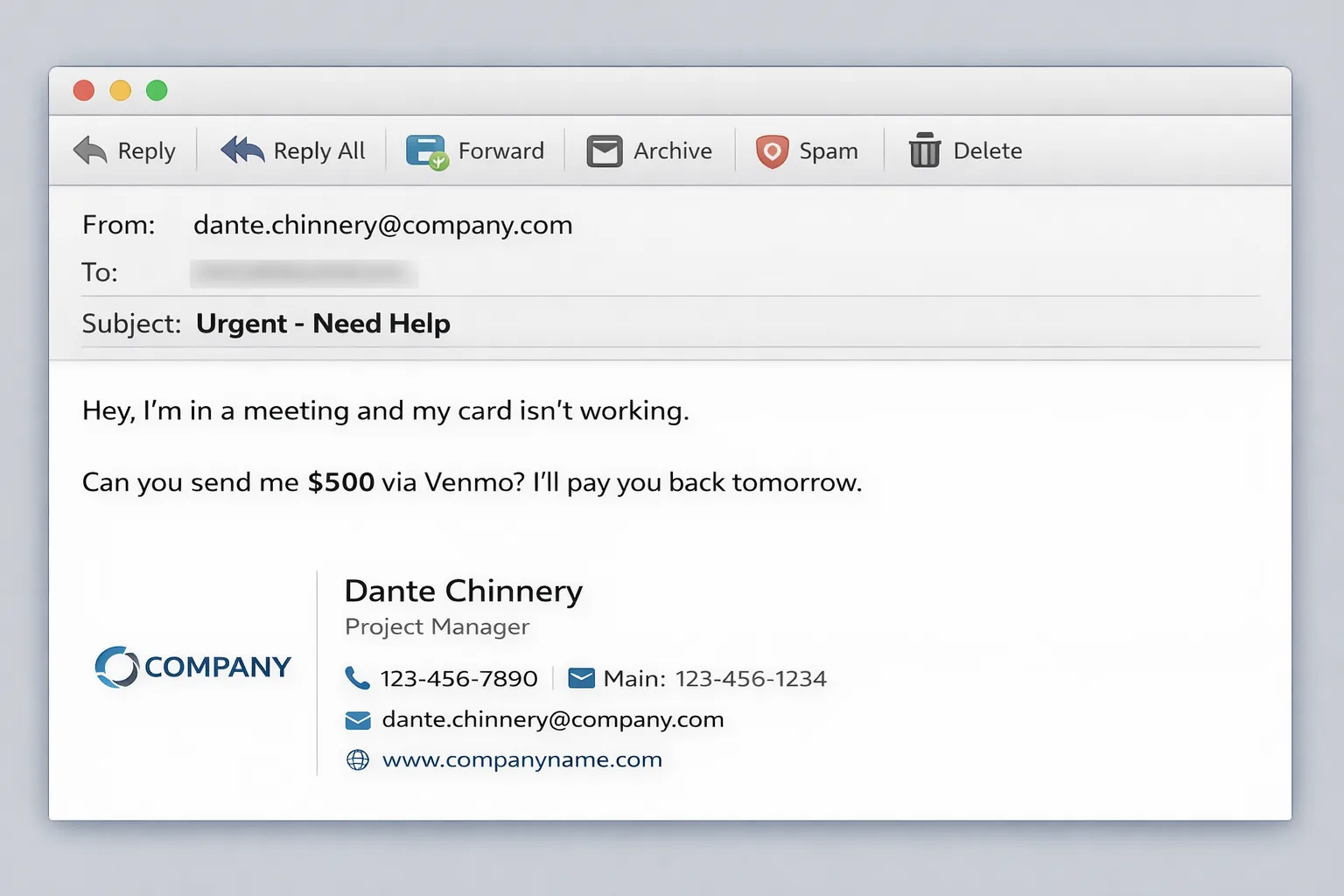
The Scenario
You receive an email from what appears to be your colleague's email address:
From: dante.chinnery@company.com
Subject: Urgent - Need Help
Message: "Hey, I'm in a meeting and my card isn't working. Can you send me $500 via Venmo? I'll pay you back tomorrow."
Without TripleValidate
Your Situation:
- Email looks legitimate - correct name and company domain
- Sounds urgent and plausible
- You want to help your colleague
- You have to guess if it's really them
- Risk of losing $500 to a scammer
Common Result: Many people send the money and realize too late it was a scam.
With TripleValidate
Step 1: Search
- Open TripleValidate
- Search: "dante.chinnery@company.com"
Step 2: Review Results
- Found: Alex Thompson, Verified Zone, ZTRS: 720
- Account active and verified
Step 3: Send Validation
- Message: "Hi Dante, I just received an email from dante.chinnery@company.com asking me to send $500. Can you confirm this is your email and you sent this request?"
Step 4: Wait for Response
If APPROVED:
- Dante confirms: "Yes, that's me! Thanks for checking."
- Safe to proceed - Send the money
If DECLINED:
- Dante responds: "No! I never sent that. My email was hacked!"
- DO NOT SEND MONEY - Report the email as phishing
If NO RESPONSE (24 hours):
- Likely a scam - Dante would respond quickly if legitimate
- DO NOT SEND MONEY - Contact Dante through other channels (phone, in-person)
Result: You saved $500 and helped identify a security breach.
Use Case 2: Wire Transfer Request
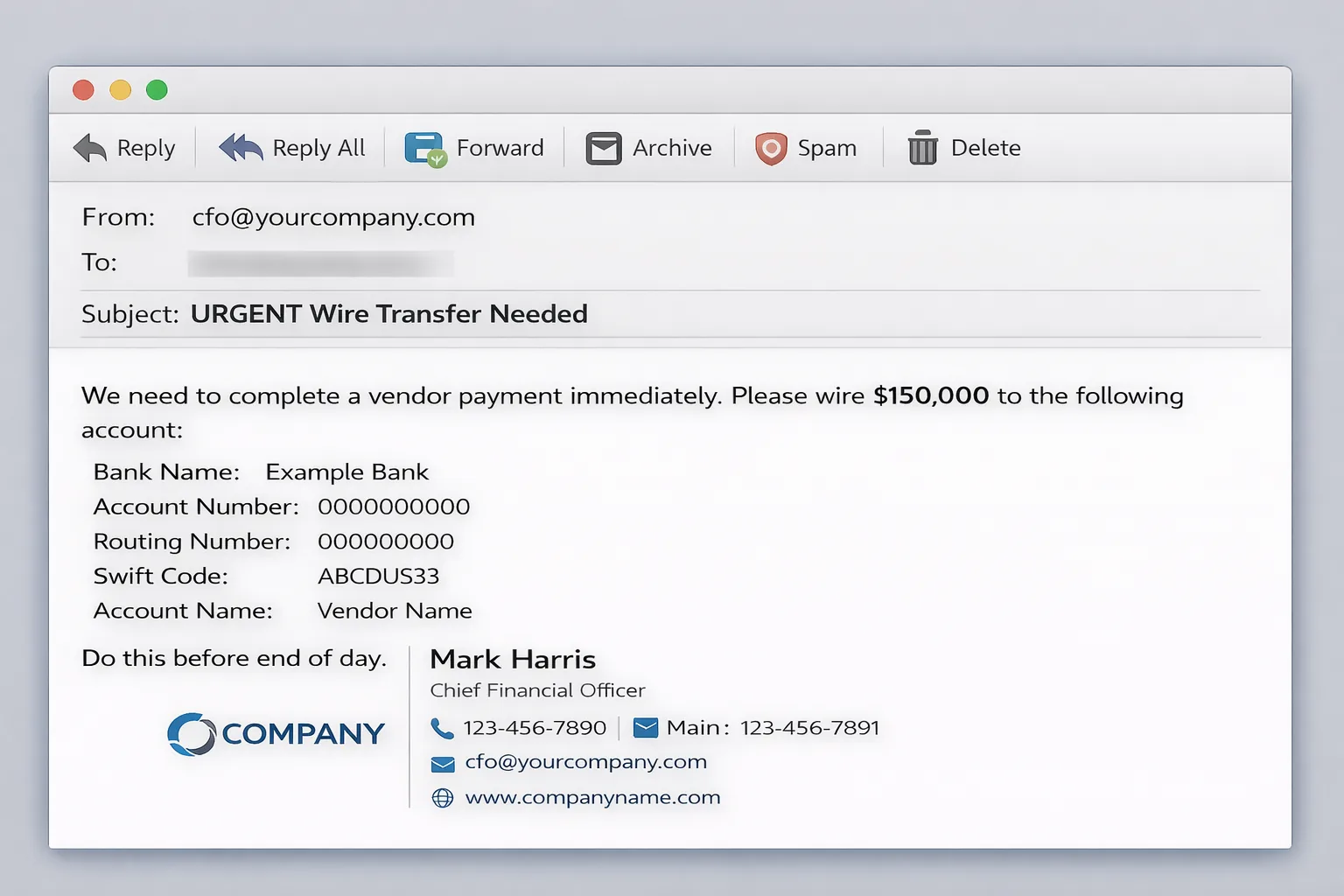
The Scenario
From: cfo@yourcompany.com (your CFO's email)
Subject: URGENT Wire Transfer Needed
Message: "We need to complete a vendor payment immediately. Please wire $150,000 to the following account: [details]. Do this before end of day."
The Danger
Business Email Compromise (BEC):
- This is one of the most expensive types of fraud
- Average loss: $125,000 per incident
- Sophisticated attackers spoof executive emails
- Creates urgency to bypass normal procedures
TripleValidate Process
Step 1: Verify the Email
- Search: "cfo@yourcompany.com"
- Check: Is this email in their TripleEnable assets?
- Review: What's their ZTRS score?
Step 2: Send Validation Request
- Message: "I received a wire transfer request for $150,000 from this email address. Can you confirm you authorized this payment and the account details are correct?"
Step 3: Evaluate Response
APPROVED:
- CFO confirms request is legitimate
- Proceed with standard wire transfer protocols
- Document the validation for audit trail
DECLINED or NO RESPONSE:
- STOP THE TRANSFER IMMEDIATELY
- Contact CFO directly by phone
- Alert IT security team
- Report the fraudulent email
- Investigate how attacker got access
Money Saved: $150,000 + hours of remediation + reputational damage
Use Case 3: Fake LinkedIn Message
A recruiter contacts you through LinkedIn. Before replying or clicking any links, run a quick TripleValidate check.
The Scenario
You receive a LinkedIn message from someone claiming to be a recruiter at a major tech company, asking for your personal information and W-2 for "background check purposes."
TripleValidate Process
Step 1: Search Their LinkedIn
- Get their LinkedIn profile URL
- Search in TripleValidate
Step 2: Review Results
If FOUND with High ZTRS:
- Legitimate recruiter in ecosystem
- Still validate before sharing sensitive info
If NOT FOUND:
- Not in TripleEnable ecosystem
- Higher risk - verify through other channels
- Check company website for recruiter directory
- Call company HR directly
Step 3: Protect Your Information
- Never share W-2 or SSN before validating identity
- Legitimate companies don't ask for this via message
- Use TripleValidate to confirm before proceeding
Use Case 4: Vendor Invoice Fraud
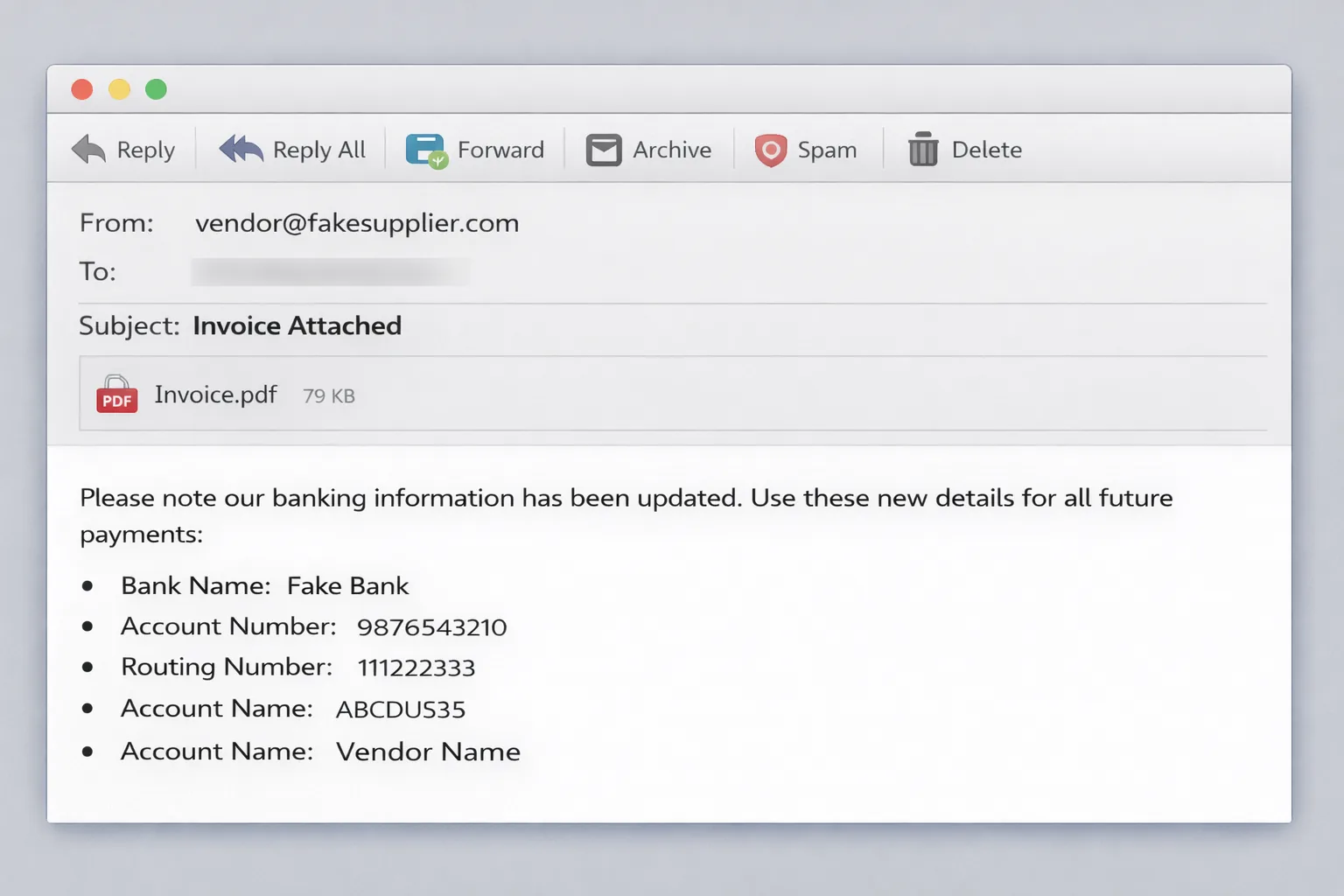
The Scenario
You receive an invoice from a regular vendor, but the bank account details have changed.
Email: "Please note our banking information has been updated. Use these new details for all future payments: [new account]"
Why This is Dangerous
Invoice Fraud Tactics:
- Attacker intercepts legitimate invoice
- Changes bank details to their account
- Sends modified invoice from spoofed email
- Payment goes to scammer instead of vendor
TripleValidate Protection
Step 1: Verify the Email
- Search the sender's email address
- Check if it matches vendor's verified assets
Step 2: Validate the Change
- Send validation: "We received notification of bank account change. Can you confirm this is legitimate and the new account details are correct?"
Step 3: Cross-Reference
- Call vendor using known phone number (not from email)
- Confirm account change verbally
- Get written confirmation with original signature
Step 4: Document Everything
- Save validation approval
- Keep audit trail
- Update vendor records
Protection: Prevents payment to fraudulent account
Use Case 5: CEO Fraud / Executive Impersonation
Someone claiming to be your CEO sends an urgent wire transfer request. This is one of the most common and costly fraud patterns.
The Scenario
From: ceo@company.com
To: You (HR Manager)
Subject: Confidential Employee Matter
Message: "I need you to process an immediate bonus payment for [employee name]. This is confidential. Send $50,000 to [account details] today. Do not discuss with anyone."
Red Flags
- Unusual request outside normal procedures
- Urgency and secrecy demanded
- CEO rarely emails directly about payroll
- Bypassing approval workflows
TripleValidate Response
Step 1: Validate Sender
- Search: ceo@company.com
- Check: Is this email in CEO's verified assets?
Step 2: Send Validation
- "I received a request to process a $50,000 bonus payment. Can you confirm you sent this and authorize this transaction?"
Step 3: Follow Protocol
- Even if validated, follow standard approval process
- Document the validation
- Get secondary approval from CFO or Board
Why This Works:
- Validates the sender identity
- Creates audit trail
- Maintains proper controls
- Protects company assets
Use Case 6: Social Media Account Verification
An account claiming to be a known brand or colleague follows you. Use TripleValidate to confirm before engaging.
The Scenario
Someone claiming to be your company's CEO sends you a direct message on Instagram asking for company financial information.
TripleValidate Process
Step 1: Search Instagram Handle
- Get the exact Instagram username
- Search in TripleValidate
Step 2: Review Results
If Instagram is Linked to CEO's Secure Zone Account:
- More likely legitimate
- Still validate before sharing sensitive info
If Instagram NOT Found or Different Account:
- Likely impersonator
- Do not engage
- Report the account
- Alert your real CEO
Step 3: Verify Through Official Channels
- Contact CEO through work email
- Use company directory contact info
- Never share company data via social media
Use Case 7: Real Estate Transaction Fraud
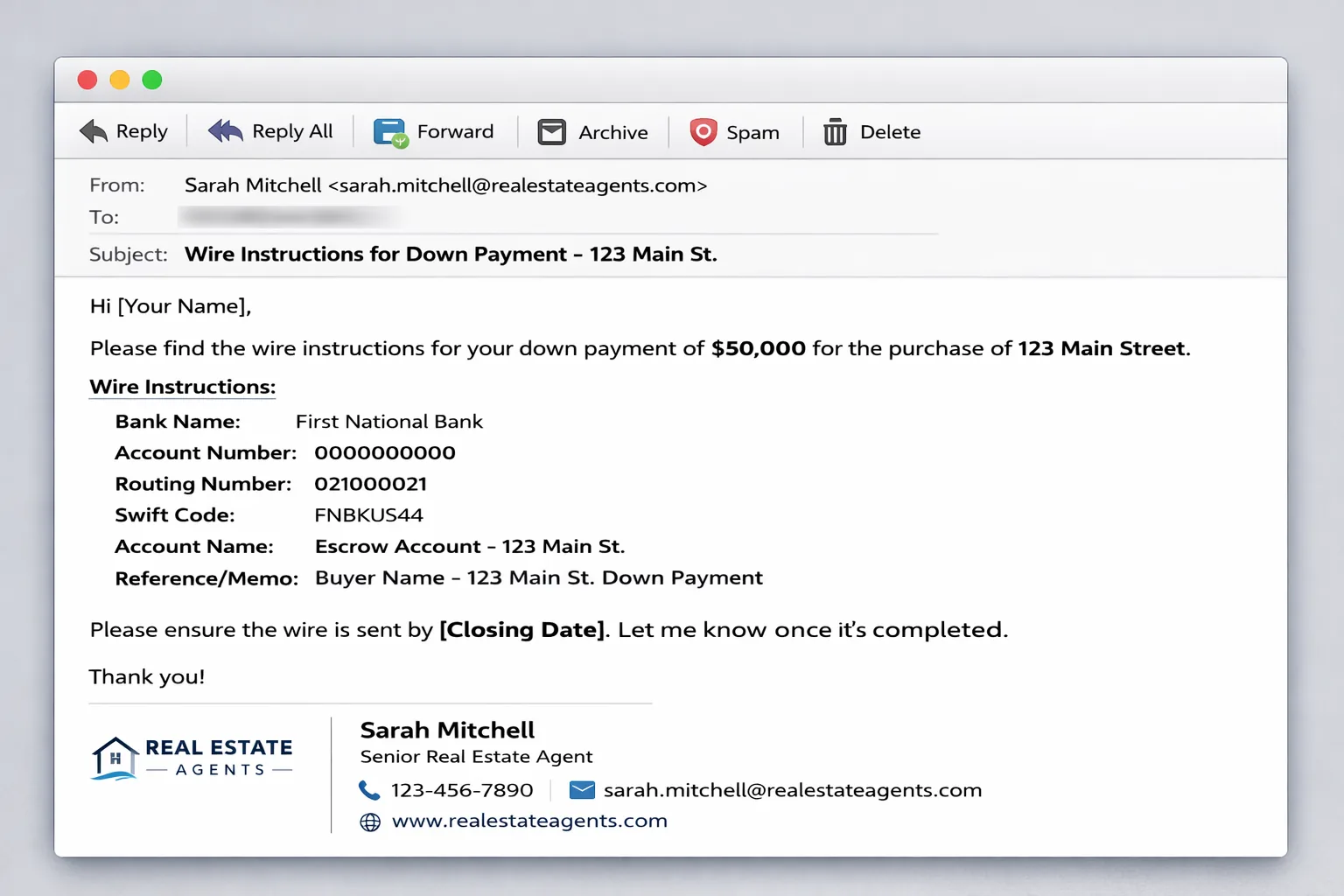
The Scenario
You're buying a house. Your real estate agent emails wire instructions for your down payment ($50,000).
High-Risk Transaction:
- Large amount of money
- Time-sensitive (closing date)
- Multiple parties involved
- Wire transfers are irreversible
TripleValidate Protection
Step 1: Verify Agent's Email
- Search agent's email address
- Confirm it matches their verified assets
Step 2: Validate Wire Instructions
- Send validation: "I received wire instructions for $50,000 down payment. Can you confirm these are the correct banking details?"
Step 3: Call to Confirm
- Even with validation approval, call agent directly
- Use phone number from business card/website
- Verify account details verbally
- Get confirmation email from title company
Step 4: Small Test Transfer
- Send $100 first
- Confirm receipt
- Then send remainder
Real-World Impact: Real estate wire fraud costs buyers an average of $150,000 per incident.
Use Case 8: Customer Support Impersonation
A message arrives claiming to be from your bank or software provider's support team.
The Scenario
You receive an email claiming to be from your bank's fraud department:
Subject: "Suspicious Activity Detected - Verify Your Account"
Message: "Click here to verify your identity and prevent account suspension."
TripleValidate Response
Step 1: DO NOT CLICK THE LINK
Step 2: Verify Sender
- Search the sender's email address
- Real banks are in Secure Zone with high ZTRS
Step 3: Contact Bank Directly
- Call number on back of your card
- Do not use contact info from email
- Ask if they sent the message
Step 4: Report Phishing
- Forward to bank's fraud team
- Report in TripleValidate (if applicable)
- Delete the email
Key Principles for All Use Cases
These principles apply regardless of the specific phishing scenario you encounter.
1. Verify Before Acting
- Never send money without validation
- Never share sensitive info without confirmation
- Never click links in suspicious emails
2. Look for Red Flags
- Urgency and pressure
- Requests to bypass procedures
- Unusual communication methods
- Grammar or spelling errors
- Generic greetings ("Dear Customer")
3. Use Multiple Verification Methods
- TripleValidate for digital verification
- Phone call for verbal confirmation
- In-person verification when possible
- Cross-reference with known contacts
4. Trust Your Instincts
- If something feels wrong, it probably is
- Take time to verify - real people will understand
- Better to be cautious than sorry
5. Document Everything
- Save validation requests and responses
- Keep audit trail of communications
- Document any suspicious activity
- Report fraud attempts
Response Decision Matrix
| Validation Result | Financial Risk | Action |
|---|---|---|
| Approved | Low | Proceed with normal caution |
| Approved | Medium (100-1K) | Proceed + secondary verification |
| Approved | High (over 1K) | Proceed + phone call + documentation |
| Declined | Any amount | STOP - Do not proceed |
| No Response | Any amount | STOP - Use alternative verification |
| Not Found | Any amount | STOP - High risk, use other channels |
Industry-Specific Use Cases
Certain industries face elevated phishing risk. These targeted approaches address sector-specific patterns.
Healthcare
- Verify patient identity before sharing medical records
- Confirm pharmacy requests for prescriptions
- Validate insurance representatives
Legal
- Verify client communications before sharing case details
- Confirm opposing counsel identity
- Validate court communications
Finance
- Verify trading instructions
- Confirm client withdrawal requests
- Validate regulatory communications
Education
- Verify parent/guardian identity
- Confirm student communications
- Validate official university communications
Next Steps
Now that you understand anti-phishing use cases:
- Searching for Identities - Advanced search techniques
- Sending Validation Requests - Best practices for effective validation
- Validation History - Track and manage your validations